Home: Multi-Computer Network Connection GEOIP Visualization
connmapperl
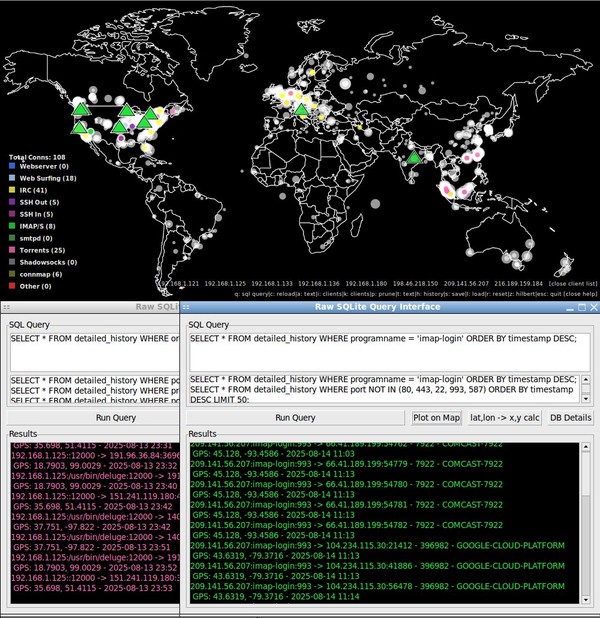
Real-time geographic visualization of all your computers' network connections — plotted on a world map, colored by type, categorized by ASN, queryable by SQL.
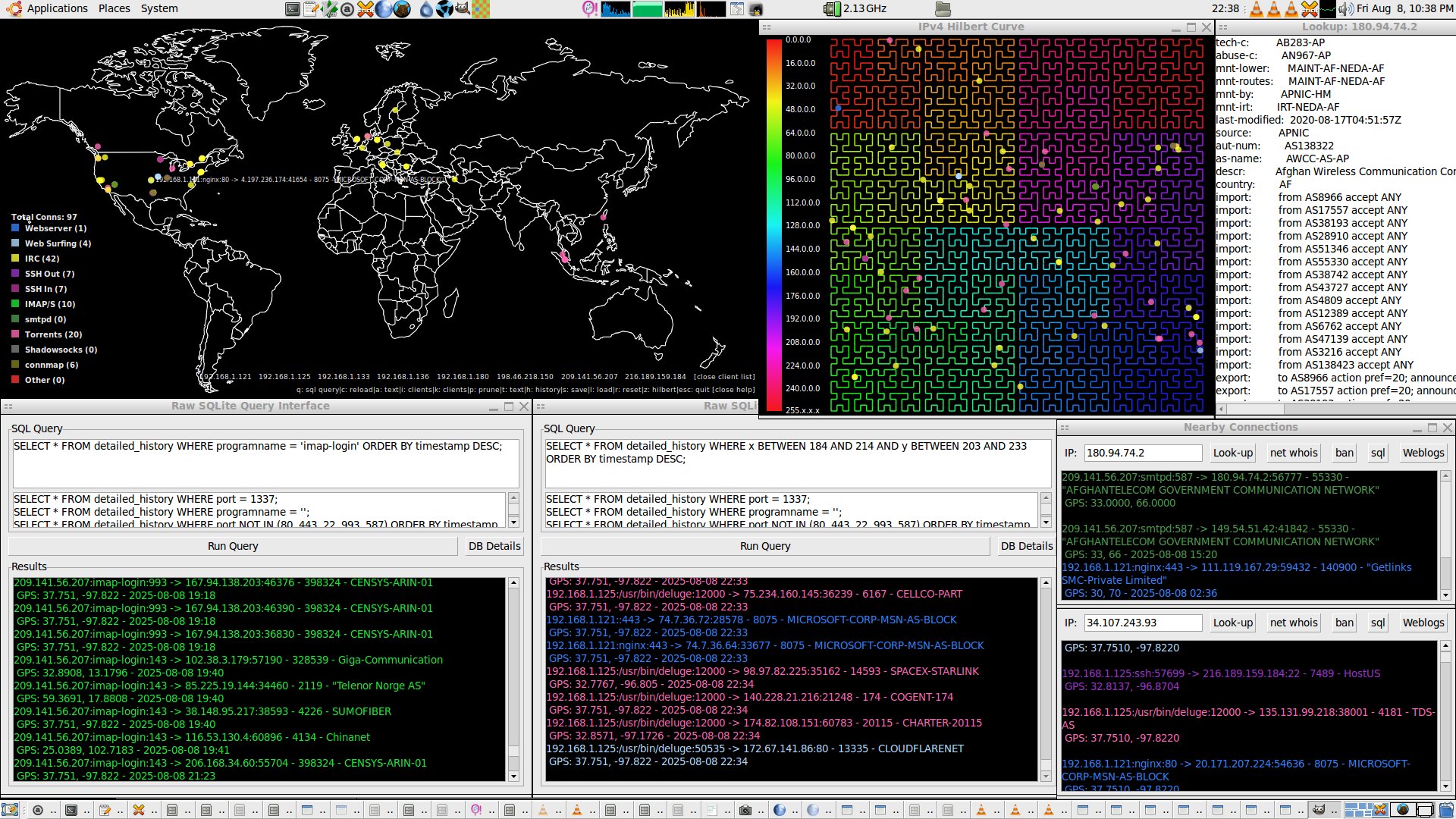
One runs connmapperl-server.pl to open the map GUI. Then a connmapperl-client.pl is run, either on the same computer, or any computer that has an IP connection. This client connects to the server GUI which then shows the geoip locations of all active connections on the computer running the client. It supports displaying many clients' active connections at once.
connmapperl.tar.gz (90MB)
The full package with everything ready to run, all the ssl certs pre-generated, registry DBs, geoip resources, etc included. Just decompress and run from inside the created folder.
connmapperl-server.pl (source)
The GUI. Runs on your desktop. Receives connection data from clients over SSL, geolocates and offline ASN look-ups each IP (via ip2asn.pl+RIR DBs), draws colored dots on a world map, and provides interactive popups, SQL history queries, and a Hilbert curve IP visualizer.
connmapperl-client.pl (source)
The headless agent. Runs on any machine you want to monitor. Every second it collects active connections with ss and streams them to the server over SSL. Reconnects automatically on disconnect.
connmapperl.tar.gz files & directories
./ ├── connmapperl-server-ssl.pl # server GUI ├── connmapperl-client-ssl.pl # headless client ├── ip2asn.pl # local whois tool ├── connmapperl2rc.beep # color rules config ├── server-cert.pem # SSL cert (auto-generated) ├── server-key.pem # SSL private key (auto-generated) ├── .connmap-history2.sqlite # detailed history DB (auto-created) ├── .connmap-history2.dat # simple history (Storable, auto-saved) └── resources/ ├── w1000-old.png # world map image (1000x500) ├── ipv4.csv # IP-lat/lon binary-search DB ├── GeoLite2-ASN-Blocks-IPv4.csv # MaxMind ASN DB ├── beep-07a.wav # alert sound (optional) ├── sorted_all-rir-delegations.txt # for ip2asn (optional) ├── caida_asn_to_name.dbm # for ip2asn (optional) ├── 20250701.as-org2info.txt # for ip2asn fallback (optional) └── *.db.aut-num # raw whois dumps (optional)
■ required ■ auto-generated ■ optional